Download iActivate
Download iActivate MDM Bypass Software for Windows or Mac computer
The business trend that started years ago and was called BYOD is still popular across the world. What is BYOD? Why is it used by small and midsize businesses? What are main advantages and disadvantages of this corporate culture? What are the best practices and policies ideas for BYOD in 2020? Let’s talk about this interesting and trendy part of IT consumerization.
The four letter abbreviation BYOD stands for bring your own device. You probably understand what BYOD means for companies and employees, still there are so many details worth your attention.
Bring your own device (BYOD) is referred to different gadgets including iPhone, iPad, other phones, tablet devices, laptops, USB drives, printers and even desktop computers. Numerous firms, companies and corporations let their employees bring their owned gadgets and use them within a business.
BYOD iPhone and iPad are among the most common examples of devices brought by workers into their workplace.
The term bring your own device (BYOD) also refers to the use for consumer apps (not only gadgets) in the workplace. There are even more specific terms such as BYOPC (related to personal computers), BYOC (related to computers), BYOL (refers to laptops) and BYOA (refers to applications).
Some firms make devices owned by employees part of their business strategy using secure and safe BYOD MDM solutions, others prefer the shadow IT system. What does it mean? Some companies let their employees use personal gadgets at work but all the apps and devices (not owned by the corporation) are not supported by its main IT department.
Both trends are used in 2020 even though there are security risks to the company in case such worker-owned devices get connected to the corporate network. It is possible to minimize the risks of users accessing important information by using BYOD MDM solutions or choosing the good BYOD policy.
What does the policy mean when it comes to companies that allow employees bringing their personal gadgets to workplace? It is a set of corporate rules that governs the level of support for such devices. As we already know, such policies can refer to mobile phones (iPhone gadgets and other handsets), computers and tablet devices as well as other innovative technique owned by workers.
It is possible to organize BYOD policies in various forms. Some companies agree to provide some money to their employees towards the equipment purchase. Still most commonly, firms agree to support gadgets already owned by their workers.
Policies can vary for different workers depending on their device, personal role in the business and other factors.
The main goal of the bring-your-own-device policy is to control the usage of personal devices at the company and minimize the possible security risks.
The whole idea of using personal gadgets for business needs has a lot of opportunities for users. At the same time there are risks of such a step for organization. Let’s talk about advantages and disadvantages of implementing BYOD strategy at work.
Small, midsize and large businesses prefer keeping an IT department within the organization. It could be a couple of employees that keep an eye on security and protection of corporate data.
Technology changes every year. New smartphones, computers and tablet devices become more powerful, bring innovative features to users and offer various apps to optimize work, save time and help developing. Employees, on the other hand, like to access corporate information from their personal gadgets and this is the main risks for the company.
Workers can work better if they are allowed to use gadgets they choose. Isn’t it more interesting to read corporate emails on the latest iPhone? Isn’t it more comfortable to read text documents on the newest iPad 2020?
The business trend has both pros and cons. Let’s mention the disadvantages and risks of bring your own device strategy. Each company has to understand all the risks related to BYOD to protect its corporate data, information, documents and apps. It could be cheaper to allow employees using their own gadgets at work but at the same time it could be expensive to support such devices and integrate them into corporate IT network.
Mobile device management solutions are one of the method of BYOD security. It is possible to add personal gadgets used at work to corporate MDM system and install special profiles to lock and control those devices.
The companies could also think about other ways of protecting their corporate documentation and data. MDM is a simple and fast solution but it adds some expenses to the company’s budget.
The popularity of mobile device management solutions for iOS devices leads to growth of sales of used iPhone and iPad models that are locked to MDM profile. Is it a big deal in 2020? Not that much. You can remove such lock and even update iOS firmware version to keep the MDM profile bypassed on any iDevice.
Rare company can afford upgrading equipment to the latest generation gadgets. Workers, on the other hand, do their job better when they have the new iPads, iPhones, Macs and other devices. It’s not surprising that the most recent iPhone matters for the business as employees are proud to perform their everyday tasks on such a gadget instead of the older office-owned device. The self-sufficiency also matters a lot.
Many companies agree with the growing role of BYOD in business development and keep implementing such strategies to motivate employees and encourage them. There are also many firms that are against BYOD idea because they feel safer when they can fully control all the corporate devices and apps used by employees.
It is impossible to stand in the path of consumerised mobility, said Ovum’s analyst Richard Absalom. This is so true. It’s better to follow the trend but keep in mind that the whole BYOD culture has its advantages and risks.

More and more iPhone and iPad users search for a reliable MDM unenroll tool which will solve MDM enrollment problem and remove restrictions and supervision […]
Read More
As a rule, when your device is enrolled into an MDM program (or Mobile Device Management program), you can view what information your employer can […]
Read More
No, there is no way for your employer to see your internet activities at home. The reasons are: a) You do not use the corporate […]
Read More
No, there is no way for your employer to see your internet activities at home. The reasons are: a) You do not use the corporate […]
Read MoreIf you want to know if your employer is tracking you, the first thing you should know is whether your iPhone or iPad is enrolled […]
Read More
Apple has a Device Enrollment Program which automates and simplifies iOS, iPadOS, macOS, and tvOS devices enrollment in MDM programs. DEP is available for devices […]
Read MoreDownload iActivate MDM Bypass Software for Windows or Mac computer
Read the most recent MDM news, how-to guides, software reviews etc.

Apple introduced the most recent iOS 17 during their annual Worldwide Developers Conference, and it became available to the public on September 18, 2023. The […]
Read More
Easiest iOS 16 MDM Bypass for iPhone and iPad Everybody who has upgraded to the latest iOS 16 can now easily bypass the MDM profile […]
Read More
Bypass Mobile Device Management Profile Activation Lock on the latest iOS 15 with iActivate! Apple just released their new iOS 15. This latest release is […]
Read More
The newest iOS version 14.7 was just released. Its beta testing lasted for several months. Apple continues fixing security issues with every new release, but, […]
Read More
iActivate team always stays tuned on the latest iOS updates and announces that MDM Bypass Software is now ready to bypass MDM on any iPhone […]
Read More
Bypass MDM Lock on any iPhone or iPad running on the latest iOS 14.4.2 with iActivate Software! Since iOS 14.4 release in September, Apple continues […]
Read More![[SOLVED] iOS 14.3 Bypass MDM](https://iactivate.host/wp-content/uploads/2020/12/ios-14-3-mdm-bypass.png)
The latest release of iOS 14.3 and iPad OS 14.3 just happened and we are happy to announce that iActivate Software is ready to bypass […]
Read More
Bypass MDM Activation Lock Screen on iOS 14.2 with iActivate! Need to bypass MDM Activation Lock Screen on iPhone running on iOS 14.2? The good […]
Read More
The step-by-step tutorial describes how to remove Remote Management (MDM profile) from iPhone. Any version of iOS and iPhone is supported! If you faced the […]
Read More
If you need to bypass MDM on the newest iOS 14 – iActivate Software is what you are looking for! Our dev team has been […]
Read More
iActivate Software is a reliable solution allowing to remove MDM Profile on any iPhone, iPad or iPod Touch model running on any iOS version, including […]
Read More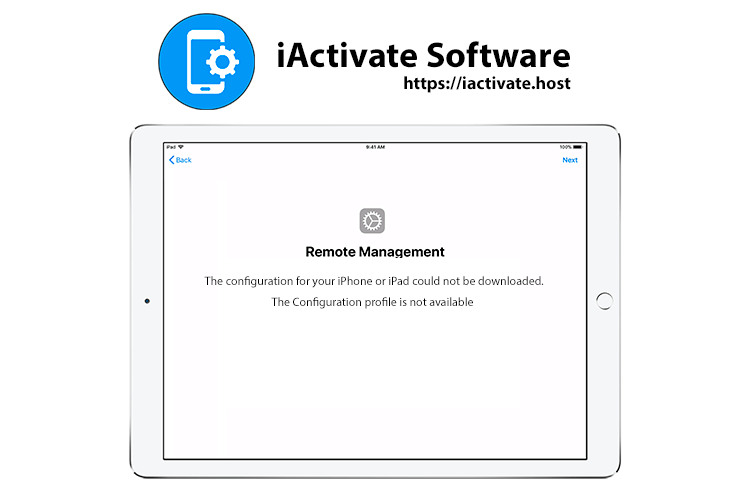
Are you ready to bypass the MDM activation lock screen on iOS 13.4-13.4.1? iActivate dev team is always following the latest updates, so we are […]
Read MoreiActivate Software is bypass solution for Supervised Apple MDM Devices